Home
Recommended
Other Links
On Ethereum block `25118335` at `2026-05-17T23:55:23Z`, attacker EOA `0x5abb91b9c01a5ed3ae762d32b236595b459d5777` called bridge dispatcher `0x71518580f36feceffe0721f06ba4703218cd7f63` and drained bridge-held assets to drainer `0x65cb8b128bf6e690761044cceca422bb239c25f9`. The trace shows a BTC-imp...
With the changes to the market of late, Atredis has actually been exceedingly busy. We've been working with AI and related tech since we started the company over a dozen years ago, but in the last year, like everyone, our work has changed: we're testing more AI, we're testing more with AI, and we
On Ethereum at 2026-05-16 18:15:23 UTC, transaction `0x99a1114c2e8dc1807e00da0e963a6fbd5d91a04d1e1fd0a75b78e9c6b41a7464` was an on-chain plaintext settlement message related to Adshares Wrapper, not the drain transaction itself. The trace shows a single zero-value `CALL` from `0xb6fe3854a85dc6c2a...
On May 16, 2026, transaction `0x7a823a891b7c5c02de50931f34cf50fc12cc600fe8b390b8f3dc29f2222c93b8` on Ethereum made a single zero-value call with plaintext calldata and no internal execution, logs, or transfers, marking it as post-incident Adshares Wrapper message traffic rather than the draining transaction.
PHP is one of the world’s most popular programming languages. The PHP core itself is rarely perceived as an attack surface — attention usually shifts to frameworks and third-party libraries. However, a significant portion of real-world application logic relies on built-in functions from the ext/standard extension, which handles strings, query parameters, data formats, and files. […]
WrappedADS on Ethereum processed a direct `wrapTo()` mint on May 15, 2026 that created `999,999.94319920782` wADS for `0x63e22ce9bde9bb8892a447258abfcaa4142f001b`. The evidence in this analysis directory supports an `access_control` conclusion, not a proven bridge-message forgery: the verified so...
On May 15, 2026, transaction 0xebeec0... on Ethereum carried a plaintext settlement demand referencing the prior TrustedVolumes theft and should be classified as post-exploit message traffic rather than the exploit itself.
The fetched artifacts show a routine Safe-mediated `unpause()` with no token transfers, no attacker gains, and no evidence of unauthorized access or exploit behavior in this transaction.
On Ethereum at 2026-05-15 14:44:59 UTC (block `25101229`), Kelp DAO's `LRTDepositPool` was unpaused through the protocol's admin Safe rather than through an exploit path. The executed action was an authorized `unpause()` administrative operation guarded by an on-chain `DEFAULT_ADMIN_ROLE` check i...
Browsers help protect some of the most sensitive data people have, including passwords. That’s why we continuously review how Edge handles that data, and where we can further reduce exposure through defense-in-depth improvements as part of Microsoft’s Secure Future Initiative (SFI).
Talk presented at Qualcomm Product Security Summit (QPSS) 2026.
The talk revisits a neglected attack surface in Android’s biometric authentication flow and explores how weaknesses around biometric AuthToken handling can be abused to crack PINs and bypass Credential Encrypted (CE) protection.
Slides available here
A retail swap on Ethereum mainnet was sandwiched on 2026-05-14 at block `25095209` by a same-address MEV bot operating around the WOJAK/WETH Uniswap V2 pair `0xcaa3a16f8440f85303afaab1992f2b97d12469b1`. The victim transaction `0xbffc57f64535df9e495c3fc0b5a5be5a8131aa1173d64f3e3ba7c9e81edf25c9` us...
Key Points Introduction The Gentlemen ransomware‑as‑a‑service (RaaS) operation is a relatively new group that emerged around mid‑2025. Its operators advertise the service across multiple underground forums, promoting their ransomware platform and inviting penetration testers and other technically skilled actors to join as affiliates. In 2026, based on victims listed on the data leak site (DLS), […]
On May 13, 2026 at 23:22:02 UTC (BNB Chain block `98134017`), attacker EOA `0xcb26b3a469c5aee911d059a25de2b26ed52826e9` executed transaction `0x2fdd6aef515fb06ce803c55086bb71de712631979809c135cf6d02be133f5cdb`, which deployed bootstrap contract `0x8aa9cb61885121448f1bf9a5df80ec36c6fbd535` and exe...
The attacker used a type-0x4 EIP-7702-authorized EOA to call Staking owner-only functions, set `stakeDays` to zero, mint fake positions with `stakeOwner()`, cash out repeated `unstake()` redemptions, and sweep remaining SQi for a final dump.
BoostHook recorded spot-priced openLong() positions without a strong post-open solvency invariant, then afterSwap() liquidated only five toxic positions because MAX_LIQS_PER_BLOCK was capped at 5, leaving additional debt exposure alive.
Exploiting the Tesla Wall Connector from its charge port connector -
Key Findings Ransomware in Q1 2026: Consolidation at Scale During the first quarter of 2026, we monitored more than 70 active data leak sites (DLS) that collectively listed 2,122 new victims. This figure represents a 12.2% decline from the Q4 2025 all-time record of 2,416 victims but remains the second-highest Q1 on record at 117% […]
The attacker used a Balancer V2 flash loan to pre-fund the treasury, then called `claimPayroll(3)` from an attacker-controlled contract that passed address-only claim authorization and triggered the treasury transfer path.
An attacker-controlled borrower opened credit requests with preApproved=false, then used a separate refreshAccount(address) transaction to move those Requested records into GoodStanding. The attacker then called drawdown(uint256) on three deprecated pools and swept the residual USDC/USDC.e balances.
The attacker initialized the proxy with malicious module addresses, causing the Renegade implementation to delegatecall attacker code in the proxy context and sweep 26 ERC-20 balances to the attacker.
CVE-2026-30815
An os command injection vulnerability exists in the Openvpn configuration restore client\_connect functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary command execution. An attacker can upload a...
CVE-2026-30815
An os command injection vulnerability exists in the Openvpn configuration restore script\_security functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary command execution. An attacker can upload...
CVE-2026-30817
An external config control vulnerability exists in the Openvpn configuration restore route\_up functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary file reading. An attacker can upload a...
On May 7, 2026, White Eagle on BNB Chain was exploited for 65,645.94 USDT through a withdrawal logic flaw that sized WEGL payouts with a manipulable live PancakeSwap quote.
On May 7, 2026, TrustedVolumes on Ethereum was drained for approximately $5.87M through an RFQ authorization design flaw that let attacker-controlled maker and signer parameters pull assets from a resolver's approved balances.
Make it Blink: Over-the-Air Exploitation of the Philips Hue Bridge
On May 5, 2026, an Ethereum victim lost 17 WBTC after a malicious callback contract routed through Ekubo flash-accounting calls to consume a pre-existing unlimited WBTC allowance.
# The Danger of Multi-SSO AWS Cognito User Pools
05 May 2026 - Posted by Francesco Lacerenza, Mohamed Ouad
After a small detour, the **CloudSecTidbits** series is back with new episodes. We had the opportunity to present them at the first DEFCON in Singapore few days ago during our DemoLabs...
"This is a writeup of my DEF CON Singapore talk that walks through vulnerabilities and exploits in M365 Copilot and Consumer Copilot. I disclosed these to …"
CVE-2025-58074
A privilege escalation vulnerability exists during the installation of Norton Secure VPN via the Microsoft Store. A low-privilege user can replace files during the installation process, which may result in deletion of arbitrary files that can lead to elevation of privileges.
The...
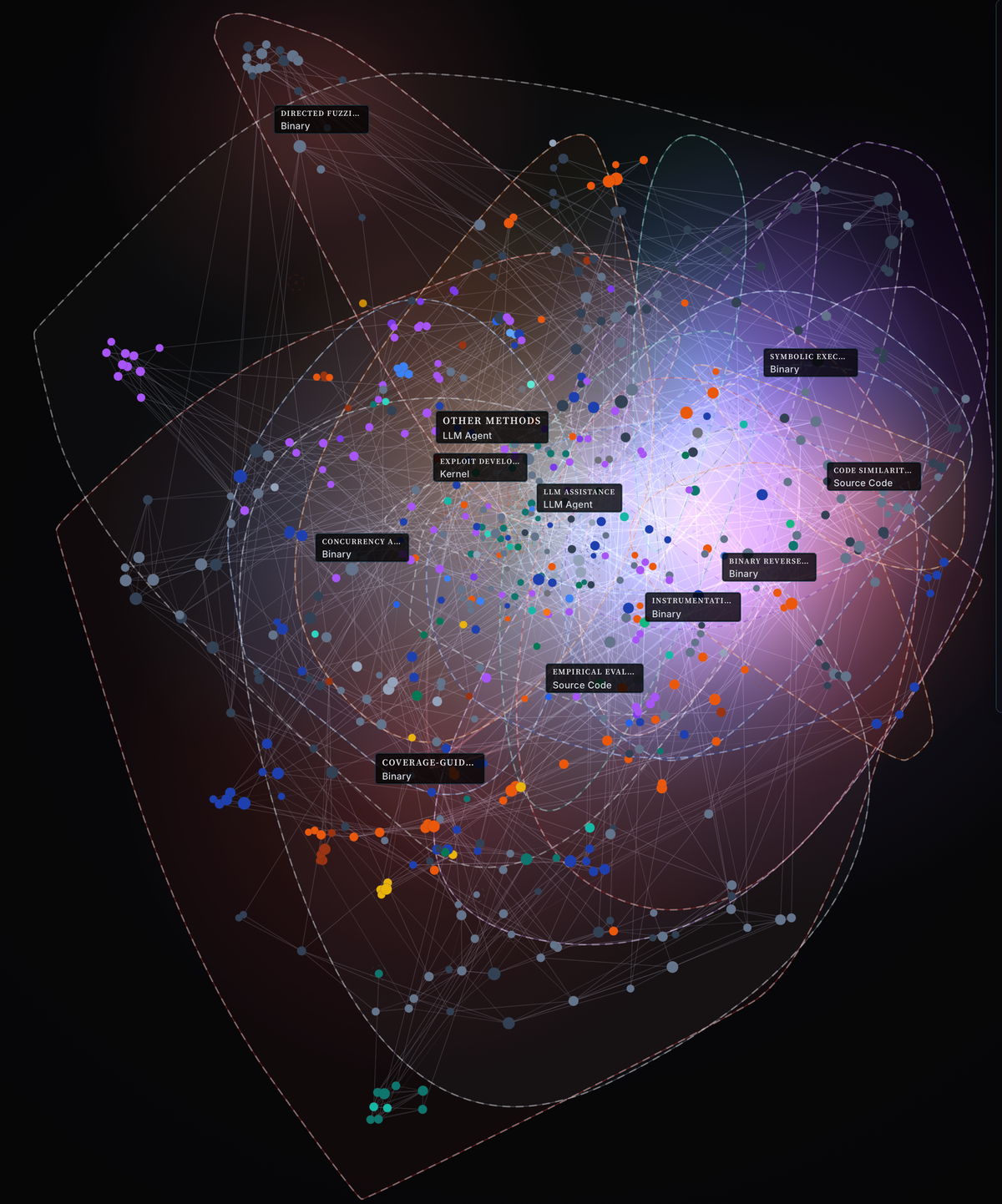
A stale security-papers README grew into AI Scholar: a production system that ingests papers, deduplicates identities, extracts structured security-research records, maps the corpus as an atlas, and surfaces tensions between papers before I read them end to end.
Some organisations’ most sensitive information is only ever discussed in person. Ironically, the equipment in meeting rooms, conference halls, and other physical locations is often among the least-monitored and most insecurely-configured attack surfaces in an organisation.
Since I published Carrot disclosure: Forgejo two days ago, numerous things happened:
- Friends of mine were reached out to, to "talk to me from a place of trust", or simply to tell them what an horrible person I am, which they found hilarious.
- The toot linking to the blogpost was removed from...
Security audit of Inspektor Gadget, an eBPF-based observability framework for Linux and Kubernetes. Sponsored by the CNCF (Cloud Native Computing Foundation), facilitated by Open Source Technology Improvement Fund (OSTIF) and performed by Shielder.
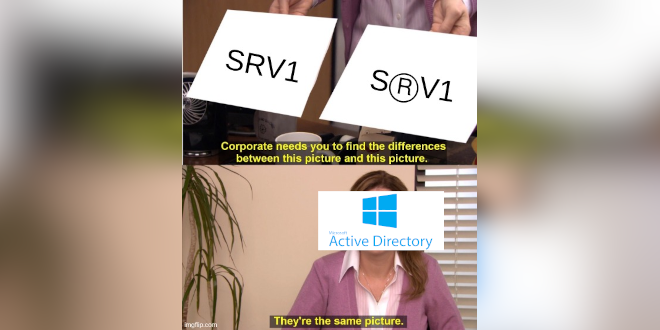
At PT SWARM, we increasingly encounter infrastructures built on alternative implementations of Microsoft Active Directory. One such alternative that has rightfully received widespread adoption is FreeIPA. I specialize in hunting for vulnerabilities in Linux infrastructures and developing red team tools. I have spoken twice at OFFZONE, where I broke down attacks against FreeIPA. Our team […]
Bypassing Windows authentication reflection mitigations for SYSTEM
Hello! Yes, it's all a disaster again!
Let's get this party started:
0:00
/0:12
1×
No comments today, so imagine this:
* We wrote something that we find very funny,
* Nobody else gets it,
* But everyone humors us
It's your typical watchTowr Labs blog introduction.
What Is cPanel & WHM?
Well, dear reader - for those that have never had the joyous experience of managing shared hosting infrastructure, cPanel and WHM are the control panel that run
On April 29, 2026, the Syndicate Commons bridge on Base was drained for 18.45M SYND after a privileged upgrade-control compromise let the attacker install malicious bridge logic and transfer the proxy's token balance.
On April 29, 2026, AftermathFi Perpetuals on Sui was exploited for roughly 1.14M USDC because fee validation allowed a negative integrator taker fee that inflated taker collateral and enabled USDC withdrawals.
TL;DR
In April 2026, Adobe disclosed three critical security issues (CVE-2026-34621,CVE-2026-34622,CVE-2026-34626) affecting Acrobat DC, Acrobat Reader DC, and Acrobat 2024. According to Adobe’s advisories, these vulnerabilities could allow attackers to execute arbitrary code and leak user information through a malicious PDF file via a prototype pollution chain and they were reportedly exploited in the wild. The initial issue, CVE-2026-34621, was first identified by EXPMON.
While several reports have already covered the threat intelligence and malware-analysis aspects of the ITW samples, we were more interested in the underlying vulnerabilities themselves and how Adobe patched them.
Since Fedora moved from Pagure to Forgejo, I finally had an incentive to take a good look at Forgejo's security posture. The results aren't pretty to be honest: SSRF in a lot of places, no CSP/Truste-Types, a bit of ghetto templating in javascript, cryptographic malpractices, overlooks in the...
Key Takeaways Background VECT Ransomware is a Ransomware-as-a-Service (RaaS) program that made its first appearance in December 2025 on a Russian-language cybercrime forum. After claiming their first two victims in January 2026, the group got back into the public eye due to an announcement of a partnership with TeamPCP, the actor behind several supply-chain attacks […]
On April 28, 2026, YieldCore's Ethereum RWAVault lost 398,655.47 USDC because overridden ERC4626 withdraw and redeem paths burned owner shares without requiring caller authorization or allowance.
TP-Link POST body stack buffer overflow
TP-Link offline password bruteforce
TP-Link HTTP authentication bypass
TP-Link POST body stack buffer overflow
TP-Link HTTP authentication bypass
TP-Link POST body heap buffer overflow